TLDR: This article explores the necessary shift from perimeter-based security to an identity-driven model to secure modern, distributed data center networking. This new approach makes infrastructure private by default and ensures connectivity only exists between explicitly authorized workloads.
Security teams face an increasingly difficult challenge. Modern applications operate across multiple environments, communicate constantly between services, and move sensitive data across networks that extend far beyond a single data center.
Despite this complexity, many infrastructure architectures still rely on a networking model built around publicly reachable IP addresses and perimeter defenses.
This model assumes that services must expose network endpoints so that other systems can reach them. Firewalls and access control rules attempt to restrict who can connect, but the underlying infrastructure remains visible to the internet.
As distributed systems grow, this approach creates a large attack surface that becomes difficult to manage.
A more secure model begins with a simple principle. Infrastructure should be private by default, and connectivity should only exist between authenticated workloads that are explicitly authorized to communicate.
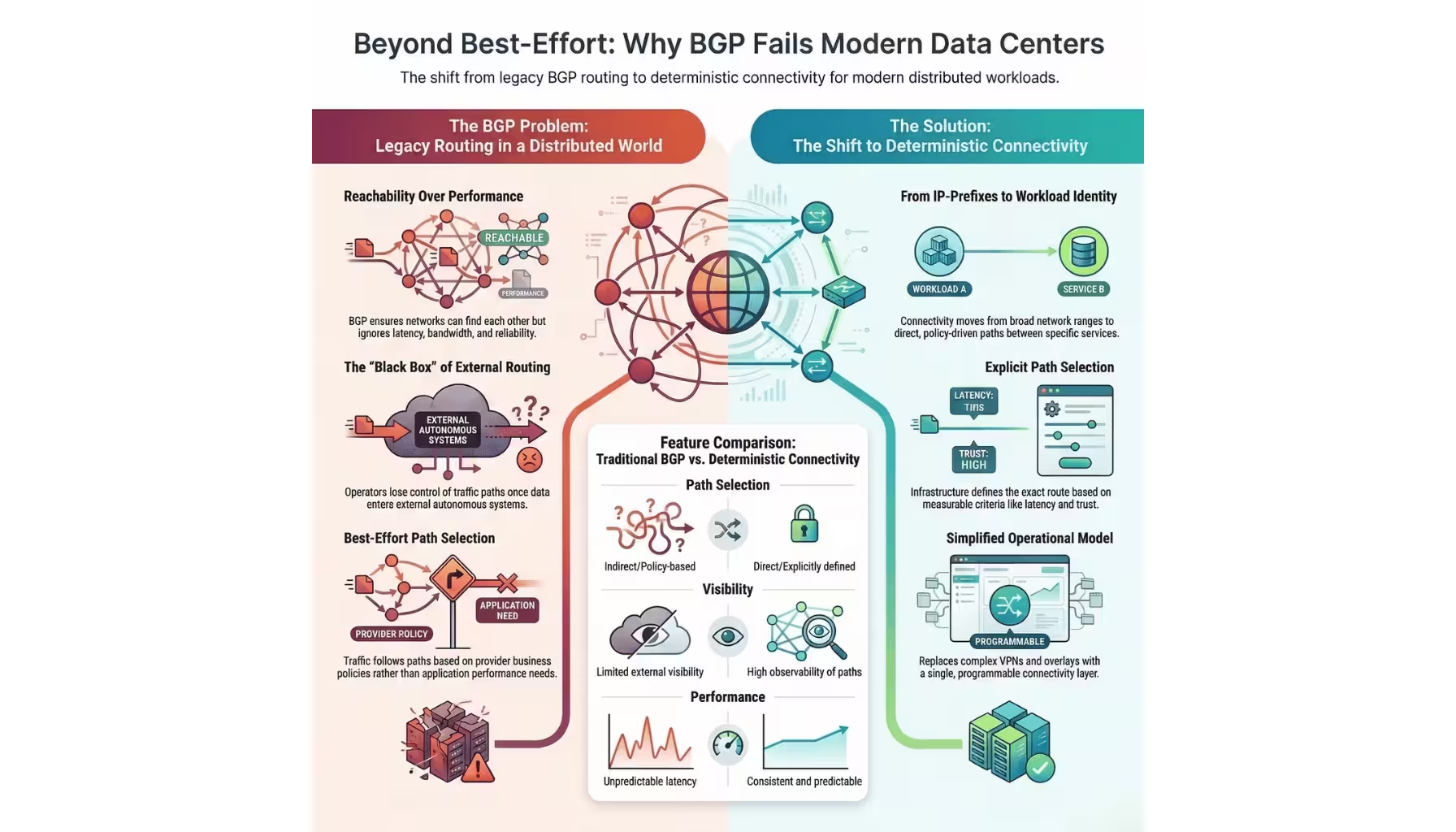
Deterministic connectivity platforms enable this shift by moving security controls from network boundaries to workload identity.
Many services inside modern infrastructure still rely on publicly reachable IP addresses, even when those services are intended only for internal communication.
For example, application services running in a cloud environment may expose endpoints through public interfaces because it is the simplest way to ensure connectivity between environments. External firewalls or access control rules then attempt to limit which systems can connect.
This approach works, but it creates several security risks.
The first risk is exposure.
Any service with a publicly reachable address can be discovered through automated internet scanning. Attackers routinely scan the global address space looking for exposed services that may contain vulnerabilities.
Even when access control rules prevent unauthorized connections, the service itself remains visible.
The second risk is configuration complexity.
Firewall rules, network access control lists, and security groups must be carefully configured to ensure that only authorized systems can connect. As the number of services grows, these rule sets become increasingly difficult to manage.
Small configuration errors can expose services unintentionally.
The third risk is dependency on network location.
Traditional security models often rely on IP address ranges or network segments to determine which systems are trusted. This assumption becomes unreliable in distributed environments where workloads move between clouds, data centers, and edge locations.
In this environment, location alone is not a reliable indicator of trust.
To reduce exposure, many organizations attempt to segment their networks into isolated zones.
Segmentation often relies on technologies such as:
Virtual local area networks that separate traffic at the switching layer.
Firewall rules that control which network segments can communicate.
Access control lists that restrict connections based on source and destination IP addresses.
These techniques can be effective within a single data center, but they become difficult to maintain across distributed infrastructure.
Modern applications often consist of dozens or even hundreds of services communicating with each other dynamically. Each service may run across multiple environments and scale up or down based on demand.
Maintaining accurate segmentation rules for this level of complexity becomes extremely challenging.
For example, an application may include front end services running in multiple cloud regions, backend processing systems located in a private data center, and analytics pipelines operating in specialized compute clusters.
Each component must communicate with specific services while remaining isolated from others.
Managing this connectivity through network segmentation requires maintaining large numbers of firewall rules and routing policies.
As infrastructure grows, these rule sets become increasingly fragile. Changes to one part of the network can inadvertently affect connectivity elsewhere.
This operational burden increases both complexity and security risk.
A more scalable security model moves the focus from network location to workload identity.
Instead of determining whether a connection should be allowed based on IP address or network segment, systems authenticate the identity of the workload attempting to communicate.
Each workload receives a unique identity that can be verified cryptographically.
When one service attempts to connect to another, both systems authenticate each other before establishing a connection. Connectivity only occurs if the identities involved are authorized to communicate according to defined security policies.
This approach provides several advantages.
First, it eliminates reliance on network location as a security boundary. A service remains protected regardless of where it runs because access decisions depend on identity rather than address space.
Second, it allows security policies to operate at the application level. Policies can specify which services are permitted to communicate rather than which network segments may exchange traffic.
Third, it simplifies policy management. Instead of maintaining large collections of firewall rules, operators define relationships between workloads directly.
As applications evolve, policies can adapt automatically to reflect those relationships.
Identity based connectivity also allows infrastructure teams to control how data moves between environments.
Traditional routing systems determine packet paths based on reachability and network policy. Operators rarely control which intermediate networks traffic traverses.
For sensitive workloads, this lack of control can create security and compliance challenges.
Organizations often need to ensure that data travels only through trusted networks or remains within specific geographic regions.
Deterministic networking platforms allow operators to enforce these requirements.
Connectivity policies can specify the networks that traffic is allowed to use, ensuring that sensitive data remains within approved infrastructure.
For example, an organization operating data centers in multiple countries may require that customer data remain within certain jurisdictions. Network policies can ensure that traffic between systems follows paths that comply with these requirements.
Similarly, operators may choose to route traffic through trusted private interconnects rather than through unknown public transit networks.
This level of control strengthens both security and compliance posture.
Moving from perimeter based security to identity based connectivity provides several operational benefits for infrastructure teams.
The most immediate benefit is a reduced attack surface.
When services are not exposed through public IP addresses, external systems cannot scan or interact with them directly. Infrastructure becomes effectively invisible to the broader internet.
Another benefit is simpler policy management.
Instead of maintaining large sets of firewall rules tied to IP addresses and network segments, operators define connectivity policies based on service relationships. These policies are easier to understand and maintain.
Infrastructure teams also gain improved visibility into communication patterns.
Because connections occur between authenticated workloads, the networking platform can track which services communicate with each other. This visibility supports security monitoring and incident investigation.
Finally, identity based connectivity aligns naturally with modern zero trust security models.
Zero trust architectures assume that no network location should automatically grant trust. Every connection must be authenticated and authorized.
Workload identity provides a foundation for implementing this principle across distributed infrastructure environments.
As applications continue to spread across clouds, data centers, and edge environments, security architectures must evolve to match this distribution.
Perimeter defenses alone cannot provide sufficient protection for systems that communicate continuously across multiple networks.
Infrastructure must instead rely on identity driven security models that protect workloads regardless of location.
Deterministic connectivity platforms such as noBGP enable this shift by establishing authenticated, encrypted connections between services and enforcing policies that control how traffic flows through the network.
The result is infrastructure that remains private by default while still supporting flexible communication between distributed workloads.
In the final article of this series, we will examine how deterministic networking and workload connectivity improve operational efficiency, reliability, and cost management for modern data center infrastructure.